How to identify a phishing scam
How to identify a phishing scam

What's coming up?
In this activity, you will learn about the different types of phishing scam. Phishing scams come in different forms, and this activity will show you how spot each kind of scam.
Start activityWhat are the most common forms of phishing scam?
Scammers use different forms of online communication to try to trick you into falling for their scam. The most common are:
- Voice calls pretending to be from legitimate companies
- Text messages that include a malicious link
- Fake web pages designed to look real
- Fake emails that seem to be from people you know or companies you trust
- Calendar invitations that come via email.


Voice call phishing scams
Voice call phishing scams will usually start with a robot call (a recorded voice) claiming to be from your bank or internet provider. The call will say there has been fraudulent activity on your account, or that there is a technical problem. If you stay on the line, a live scammer will take over the call and try to trick you into giving them access to your computer and personal information.
Text message phishing scams
You will receive a text message on your smartphones that claims to be from the government or an institution such as your bank or insurance company.
The text message will say there’s a problem with your account or details and will ask you to tap on a web link included in the message. This will take you to a website that appears to be legitimate that will try to trick you into revealing personal information.
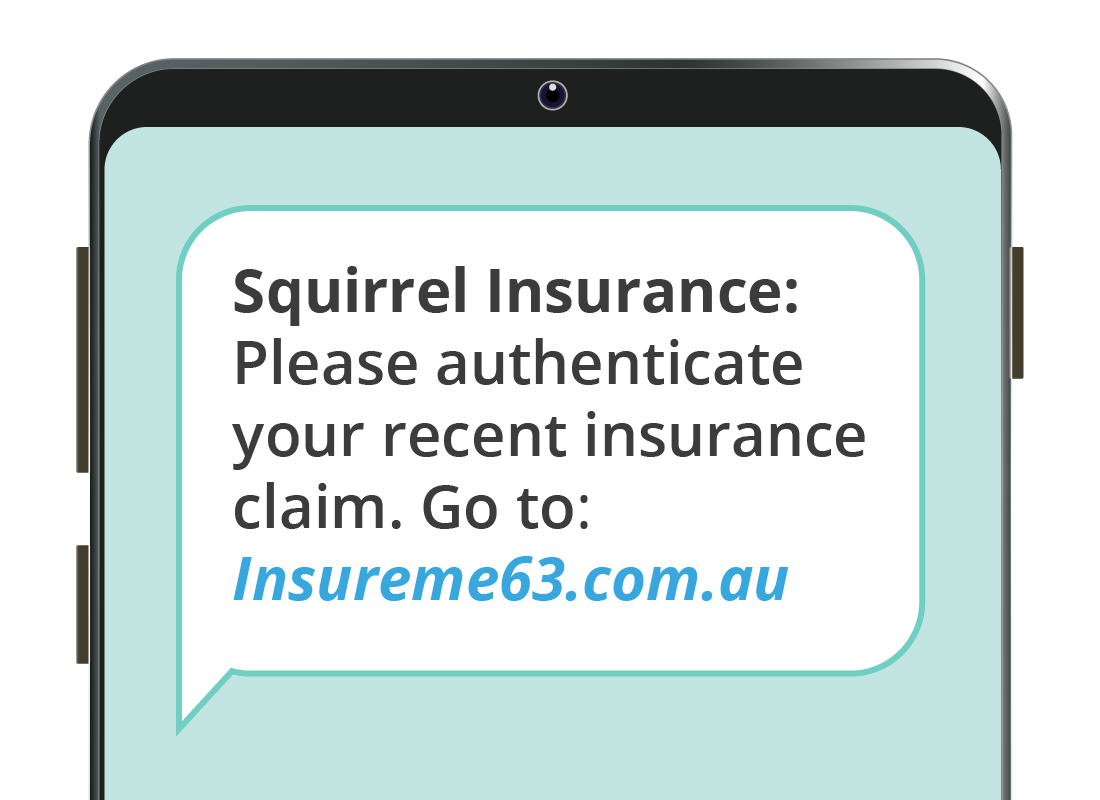
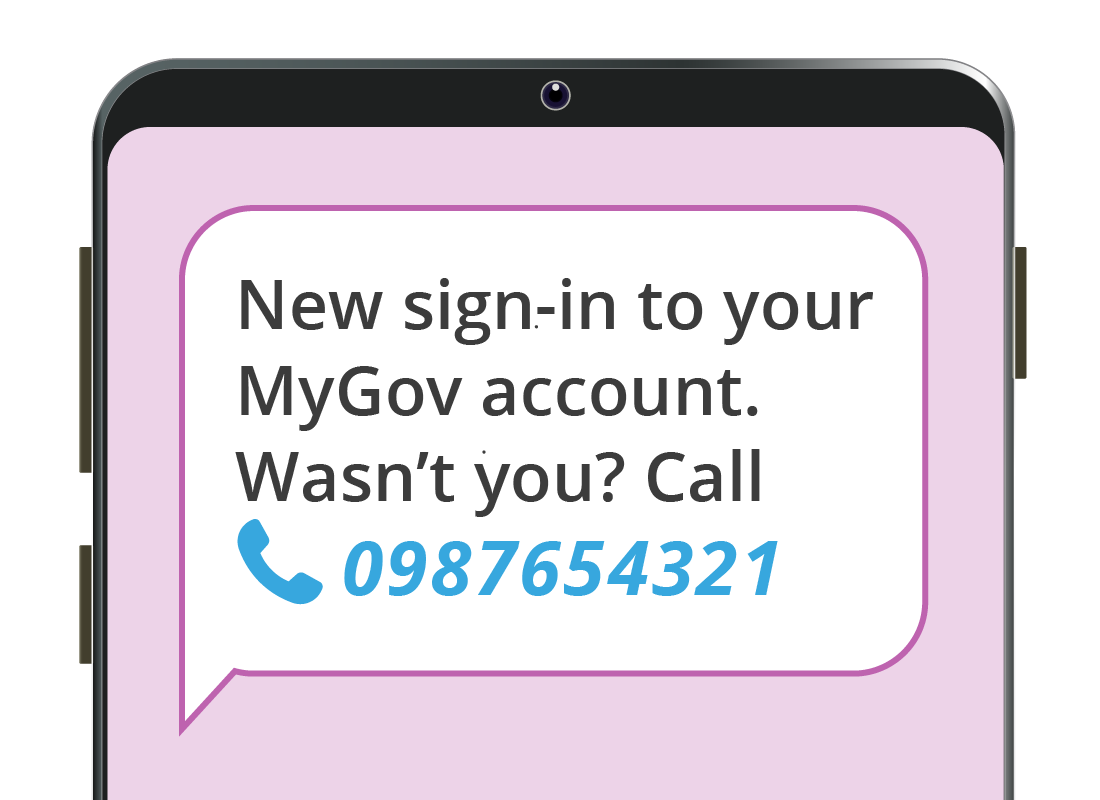
Text message phishing scams...continued
Some text message phishing scams will ask you to call a number, where the scammer who answers will try to get you to purchase something or provide your personal details.

eSafety tip
Unlike your computer’s web browser, your smartphone web browser often won’t show the full web address (or URL) of the site you are visiting. This makes it vulnerable to phishing scams, because the site may look legitimate but have a different address to the real website, which you can’t easily check.
It's best to avoid tapping on any link that’s sent to you in a text message.
Fake web page phishing scams
Scammers can design a web page to look identical to the official page of your bank, internet provider or even an e-store like Amazon. This page will include boxes for you to enter your email and password, or details such as your date of birth, answers to secret questions, or address. All this information will then be stolen by the scammer.
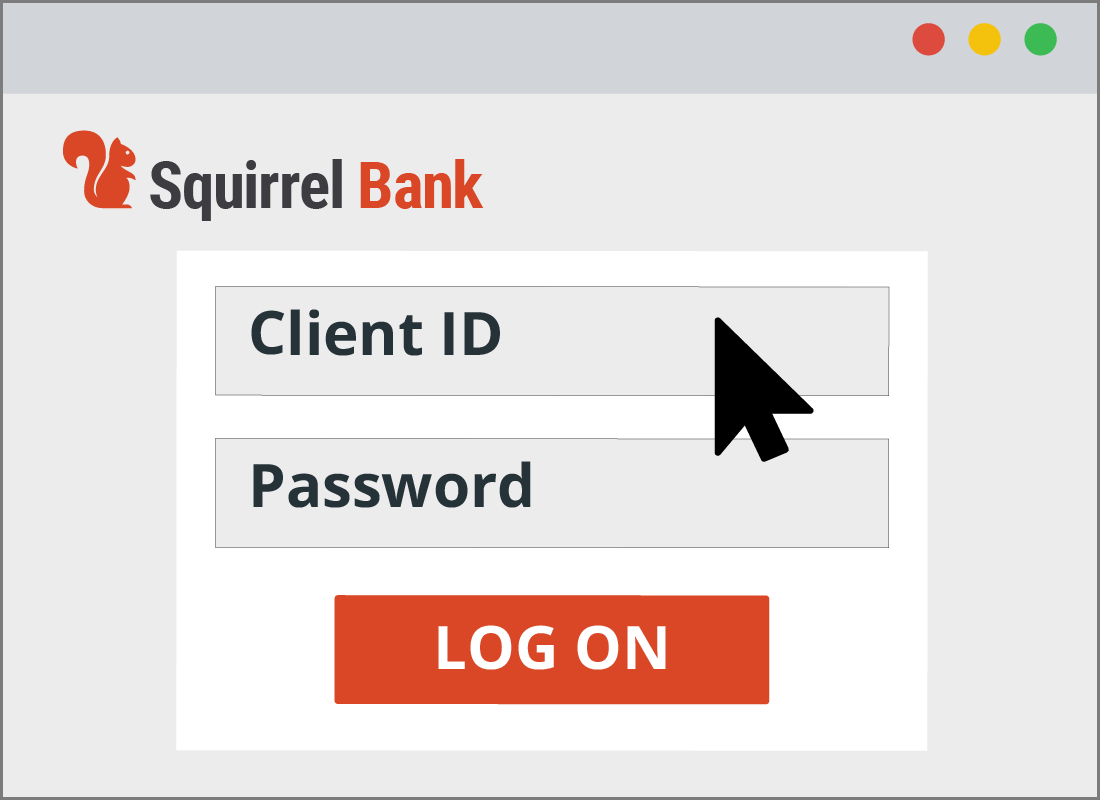

Fake web page phishing scams...continued
Fake web page scams work because the address of the fake site will be slightly different to the real address. For example, Squirrel Bank might have a web page at www.squirrelbank.com.au and the scammers will use www.squirelbank.com.
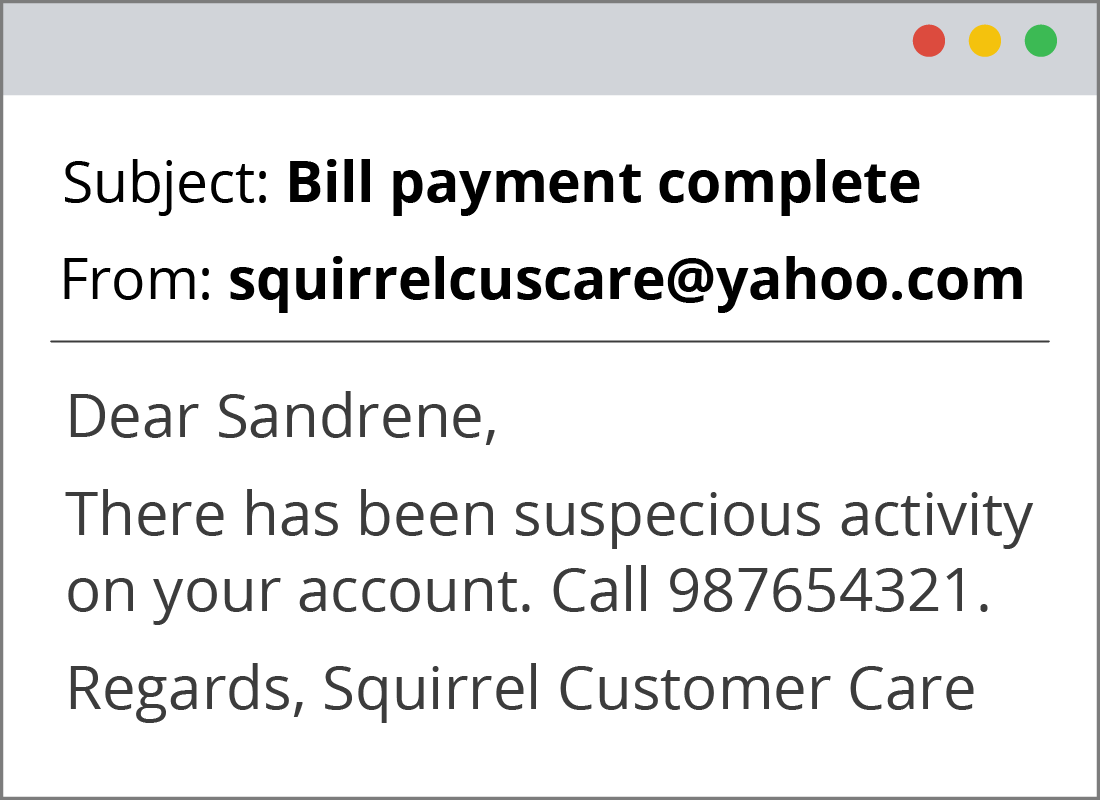
Fake email phishing scams
Scammers can design emails to look like they have come from a legitimate company, institution, or even a friend. These emails include a link to a fake web page, or may ask you to call a number, where you’ll be speaking to a scammer.
Like a fake website, the email address of the fake email will be different to the real email address used by that company or institution. For example, instead of customercare@squirrelbank.com.au the address might be squirrelcustomercare@yahoo.com.

Calendar invite phishing scams
Calendar invites rely on the recipient having an email account linked to a calendar app (such as Gmail and Google Calendar). When a scammer sends a calendar invite, instead of it appearing as an email you can delete right away, it gets added automatically as an event in your calendar.
Calendar invite phishing scams...continued
When the day of the event arrives, you might get a notification that includes a link. Since it is from your own calendar, you might not realise the link will take you to a fake website or install malicious software on your computer.

Well done!
This is the end of the How to identify a phishing scam activity. You’ve learned about some of the various types of phishing scams and how they work.
Up next, you can find out how to avoid being tricked by these scams in the Protecting yourself from phishing scams activity.
